Browser fingerprinting is a powerful technique that websites use to identify users by collecting a variety of data points, such as fonts, screen resolution, time zone, plugins, audio setup, and overall configuration.
But the real question is, how exactly can you check and read your own browser fingerprint? And how do you know if it’s going to raise red flags on the websites you visit? There are a couple of tools available for that, such as Pixelscan.
In this article, we’ll go through all the key aspects of Pixelscan in detail to determine if it’s the right solution to analyze your browser fingerprint.
What Is a Browser Fingerprint?
A browser fingerprint is a unique identifier that is generated by collecting information regarding a user’s specific configurations, hardware details, and software settings of a web browser. Operating systems, installed fonts, and screen resolutions are some of the key data points collected in this regard.
You can learn more about the working and components of browser fingerprinting in our detailed guide.
Now that you know about the basics of what a browser fingerprint is, let’s look at one of the best tools to check and read it.
What Is Pixelscan?
Pixelscan is a free digital fingerprint tool that helps you determine what websites see when you visit them. It works as a reliable browser fingerprinting analysis and security check tool to get complete insights into the key aspects of a user’s browser. The tool can also detect residential IP addresses and geolocations.
It is used by proxy users who need to verify that their IP, timezone, and geolocation are all in alignment. It is also used by antidetect browser operators who want to confirm that their spoofed parameters are holding up under inspection. And it is used by everyday users who simply want to understand what information their browser is giving away.
While there are multiple other browser fingerprinting analysis tools (such as BrowserScan, CreepJS, and AmIUnique), Pixelscan stands out as a modern and efficient tool that provides comprehensive data about both mobile and desktop browsers by combining IP detection, bot detection, DNS leak testing, and full fingerprint analysis into a single interface.
How Does Pixelscan Work?
Pixelscan performs a comprehensive browser fingerprint test to analyze a number of signals used by websites to identify visitors. When you load the page, the tool executes a series of JavaScript-based tests directly in your browser. It does not install anything or require an account. The scan examines multiple data points, including:
- Canvas rendering
- Installed fonts
- WebGL
- Software configurations
- HTTP headers
- Audio context
It is common for many people to assume that these signals are insufficient to provide any concrete data about a user. Such an assumption is only right if you are looking at the data points individually. But when the analysis of these signals is combined, it is possible to create a unique browser fingerprint that differentiates your device from the others.
The core logic is about consistency. If your browser claims to be Chrome on Windows, but your canvas rendering matches a Mac GPU, or your timezone says UTC+3 while your IP address geolocates to New York, those mismatches get flagged. Pixelscan is looking for contradictions between parameters that should agree with each other.
What Does a Browser Fingerprint Test Include?
Pixelscan goes much deeper than other browser fingerprinting analysis and detection tools. It analyzes your browser environment across different metrics and categories. Let’s look at them one by one.
Canvas Fingerprint
Every browser has a hidden graphic being rendered in the background. The hash generated by such graphics is unique to your hardware and software. Pixelscan can analyze your canvas fingerprint to detect spoofing and rendering noise.
If you are using an antidetect browser that spoofs your canvas, Pixelscan will tell you whether the spoofed output looks natural or whether it introduces rendering noise that detection systems would flag.
Audio Fingerprint
Pixelscan uses the browser’s AudioContext API to measure how your browser processes sound. Even small details here can help the tool identify your exact machine, or at least, narrow it down to some models.
Audio fingerprinting is harder to spoof convincingly than canvas. Many antidetect browsers handle canvas spoofing well but end up leaking real audio signatures. Pixelscan is able to catch this type of inconsistency.
WebGL Properties
GPU vendor, renderer strings, and extension usage are some of the key metrics analyzed as part of the WebGL fingerprint. Pixelscan reads these values and checks them for consistency with the rest of your reported environment.
For example, if your user-agent says you are on an iPhone but your WebGL renderer reports an NVIDIA desktop GPU, detection systems will flag the mismatch immediately. This is one of the most common configuration errors that occurs when using antidetect browsers.
OS Settings
Pixelscan also reads browser and OS headers that include user-agent information, language inputs, platform strings, and encoding. The information here should match the rest of your browser fingerprint.
For example, if your user-agent says “Android” but the screen dimensions are of a desktop, there’s likely to be an issue with your configuration, or maybe you are trying to spoof OS and browser fingerprint intentionally.
Timezone
If there’s a mismatch between your set language and timezone, Pixelscan is likely to flag it. Different platforms also often notice this because it’s a common sign of spoofing.
This is particularly important for proxy users. If you are connected through a residential proxy in Germany but your browser timezone is set to America/New_York and your language is en-US, websites will notice the inconsistency. This is one of the most common reasons proxy users get flagged, and it is also one of the easiest issues to fix.
IP and Geolocation
Pixelscan detects your visible IP address, determines whether it belongs to a datacenter, residential ISP, or mobile carrier, and maps it to a geographic location. It also checks against known proxy and VPN blacklists.
For proxy users, this section is especially important. It tells you whether your proxy IP is “clean” (not blacklisted), whether it is being correctly identified as residential or mobile, and whether its geolocation matches the rest of your browser environment.
WebRTC Leak Test
Pixelscan also checks for WebRTC leaks, which is one of the most common ways a real IP address gets exposed even when a proxy or VPN is active. WebRTC is a browser protocol used for real-time communication, and if it is not properly configured, it can bypass your proxy and reveal your actual IP to websites. This is a critical check for anyone using proxies who wants to ensure their real location stays hidden.
Key Features and Benefits of Pixelscan
The above sections paint a good picture of why you should use Pixelscan to check and read your browser fingerprint. Nevertheless, let’s take a closer look at the key features and benefits of Pixelscan.
| Feature | Description | Benefit |
|---|---|---|
| Browser Fingerprint Test | Evaluates your settings and browser’s profile to create a unique ID | Useful to identify privacy risks |
| JavaScript Analysis | Analyze a browser’s JavaScript settings | Discover tracking channels |
| Analyze Hardware Configuration | Scan and analyze the device’s characteristics, such as GPU, CPU, and screen resolution | Make sure your browser is aligned with the hardware |
| Track IP Address | Determine IP address and geolocation | Beneficial in identifying location exposure risks |
| Configuration Checks | Analyze browser settings and inconsistencies | Determine and remove misconfigurations |
| Bot Detection Flags | Checks for automation markers (navigator.webdriver, etc.) | Verify your headless browser or automation setup is not exposed |
| WebRTC Leak Test | Detects if your real IP is exposed through WebRTC | Ensures your proxy is not being bypassed |
| DNS Leak Test | Checks if DNS queries are leaking to your ISP | Confirms your traffic is fully routed through the proxy |
How to Use Pixelscan to Check and Read Browser Fingerprint?
Let’s go through the step-by-step guide on how to use the Pixelscan fingerprint analytics tool.
Step 1: Open Pixelscan
Open the official website of Pixelscan in your web browser. You can access the website on both mobile and desktop browsers. If you are testing a proxy or antidetect browser configuration, make sure the proxy is active and the antidetect profile is loaded before opening the page.
Step 2: Start Browser Fingerprint Test
Click on the Scan My Browser Now button to start the browser fingerprint test and get a complete picture of your digital footprint.
Step 3: Review the Results
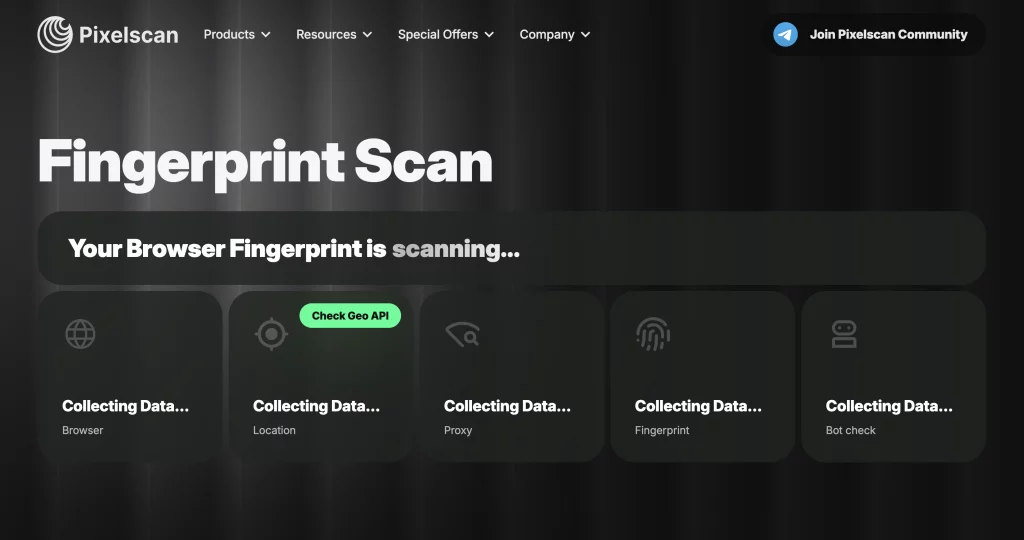
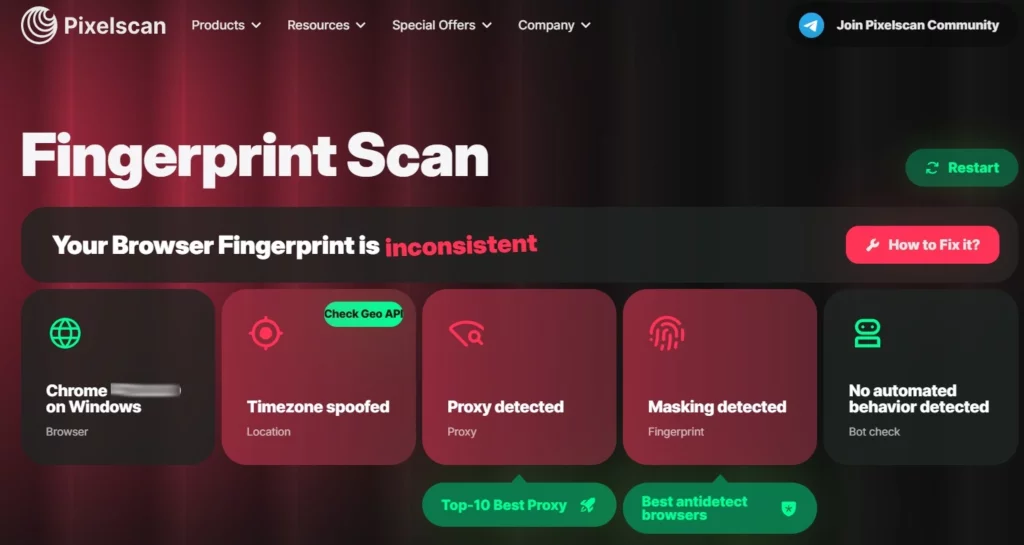
Pixelscan will take a few seconds to fully analyze your browser. Once done, you can review the results, including the name of your browser and device, location, proxy detection, masking, and web automation behaviour.
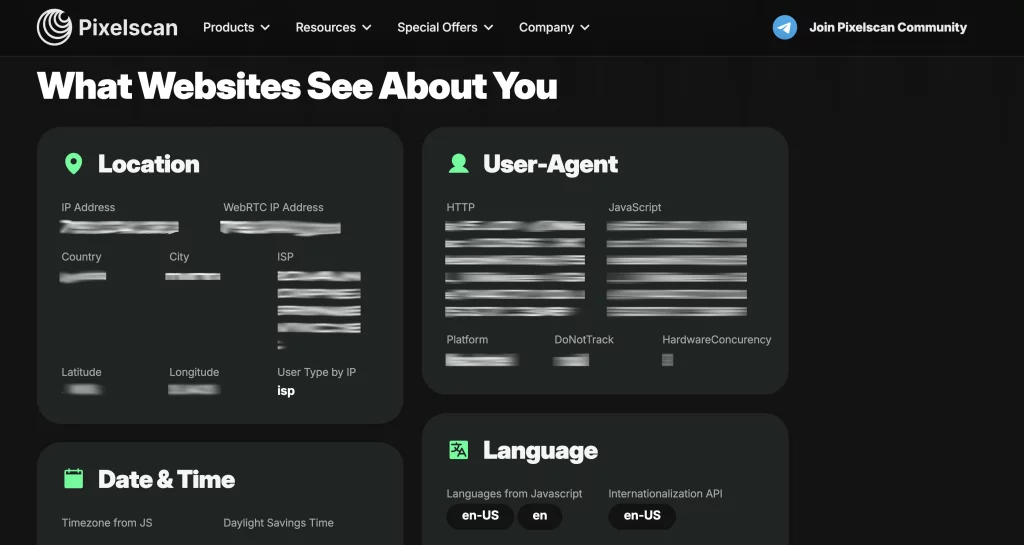
You can also review your browser fingerprint in detail to see exactly what websites see about you.
Step 4: Explore Other Tools
Pixelscan is not limited to only performing the browser fingerprint test. You can also explore other tools in it, such as IP address check, bot verification, VPN check, DNS leak test, and WebRTC leak test.
Understanding the Results of a Browser Fingerprint Test
In addition to getting a list of parameters, you’ll also get a clear and specific result after performing a browser fingerprint test using Pixelscan. Here’s what it means:
Consistent is the default state of a digital browser fingerprint. It means all of the evaluated metrics are in alignment, and the system has not raised any red flags regarding your browser fingerprints. This is the result you want when running a proxy or antidetect browser setup in production.
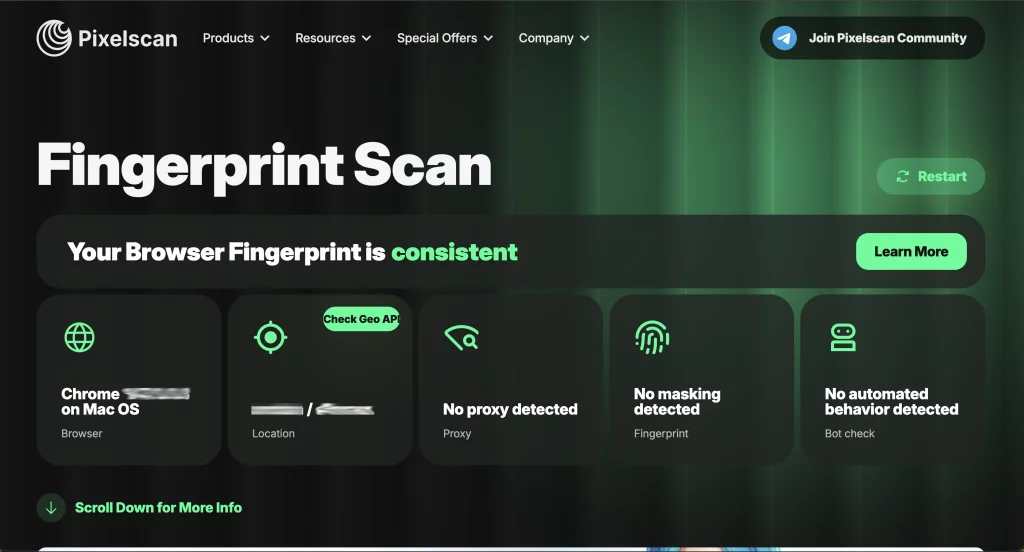
Inconsistent results can be considered as “fail” in a browser fingerprint test. It means there are mismatches in your browser fingerprints. For example, it can happen when the IP address does not match the geolocation, or there are contradictions between other parameters.
Common causes of an inconsistent result include:
- Your proxy IP geolocates to a different country than your browser timezone
- Your user-agent claims a different OS than your canvas/WebGL rendering suggests
- Your antidetect browser is spoofing canvas but leaking real audio or WebGL data
- Navigator.webdriver is set to true (common in default Selenium/Playwright setups)
- Your language and locale settings do not match your IP location
- WebRTC is leaking your real IP address despite having a proxy active
It is important to note that mismatches are not always critical individually, but since Pixelscan analyzes the fingerprint as a whole, they can result in your profile being considered suspicious, especially if you are not using good-quality mobile proxies that align with your browser configuration.
How to Fix an Inconsistent Browser Fingerprint
If Pixelscan returns an inconsistent result, here is how to approach fixing it based on the type of mismatch you are dealing with.
IP and Timezone Mismatch
This is the most common issue for proxy users. Your proxy routes traffic through one country, but your browser timezone is still set to your real location.
To fix this, you need to set your browser timezone to match your proxy’s geolocation. In antidetect browsers like GoLogin, Dolphin Anty, or Incogniton, this is typically set within the browser profile configuration. If you are using a raw browser with a proxy, you will need to manually adjust the timezone or use a browser extension to override it.
IP Type Detection
If Pixelscan flags your IP as “datacenter” or shows it on a blacklist, the issue is proxy quality rather than browser configuration.
To fix this, consider switching from datacenter proxies to residential or mobile proxies. Mobile proxies in particular carry the highest trust scores because mobile carrier IPs are shared among many real users via CGNAT, making them nearly impossible for websites to block without affecting legitimate traffic.
WebGL or Canvas Mismatch
If your fingerprint shows a GPU or rendering signature that contradicts your claimed operating system or device, your antidetect browser profile is likely misconfigured.
To fix this, ensure your antidetect browser profile matches a real device configuration. You should not claim to be an iPhone while using a Windows desktop GPU. Most modern antidetect browsers provide pre-built profiles that handle this automatically, but manual profiles require careful attention to hardware consistency.
WebRTC Leak
If Pixelscan shows your real IP address is being exposed through WebRTC, your proxy is being bypassed for certain types of browser connections.
To fix this, disable WebRTC in your browser settings or use an antidetect browser that blocks WebRTC leaks by default. In Firefox, you can set media.peerconnection.enabled to false in about:config. In Chrome-based browsers, you will need an extension or an antidetect browser profile that handles this automatically.
Bot Detection Flags
If Pixelscan detects automation markers, your headless browser or Selenium/Playwright instance is exposing itself as automated.
To fix this, use a stealth plugin or an antidetect browser that suppresses automation indicators by default. For Python users, the playwright-stealth package (v2.x, actively maintained) is the current standard. For Puppeteer users, puppeteer-extra-plugin-stealth remains widely used, though it has not received a new release since 2023 and its effectiveness has declined against newer detection systems. In both cases, make sure that navigator.webdriver is not set to true in your configuration.
Pixelscan vs Other Fingerprint Checking Tools
While Pixelscan is an excellent all-in-one solution, it is worth knowing how it compares to other options available in the market.
| Tool | Strengths | Limitations |
|---|---|---|
| Pixelscan | All-in-one (fingerprint + IP + bot detection + DNS/WebRTC leak tests), clean UI, free | Does not test every possible fingerprinting vector |
| BrowserScan | Detailed fingerprint breakdown with authenticity scoring, includes bot detection, Proxidize partner | Less comprehensive on IP/proxy analysis and leak testing |
| CreepJS | Most technically thorough fingerprint analysis, open source | Difficult to interpret for non-technical users, no IP or proxy checks |
| AmIUnique | Academic research-backed (INRIA), large dataset, analyzes 80+ dimensions | Interface is dated, limited actionable guidance for fixing issues |
For most proxy and antidetect browser users, Pixelscan provides the right balance of comprehensiveness and usability. If you need deeper technical analysis of specific fingerprinting vectors, CreepJS is the more thorough (but less accessible) option. If you want a detailed authenticity score for your antidetect browser profile, BrowserScan is a strong complement to Pixelscan.
Conclusion
Pixelscan is a great addition to the browser fingerprinting industry. It has a special place in the market because it combines multiple types of tests, such as IP detection, bot detection, WebRTC and DNS leak tests, and full fingerprint analysis, into one free and user-friendly tool.
Overall, Pixelscan is a reliable browser fingerprint analytical and detection tool. It is useful not only for the experts and security analysts, but also for proxy users who want to verify their setup passes inspection and everyday users who want to check and read their digital footprint and determine how websites view the information obtained via browsers.
The tool is most valuable when used as part of a setup verification workflow: configure your proxy and antidetect browser profile, run Pixelscan, check for inconsistencies, fix any mismatches, and re-test until everything is aligned. This process takes minutes and can prevent hours of troubleshooting failed requests and unexpected blocks.
Key Takeaways
- A unique identifier generated by collecting the user’s configurations, like hardware details, software information, screen resolution, and audio data, is called a browser fingerprint.
- Pixelscan is a powerful and free tool to analyze, view, and understand your browser fingerprint and determine if your digital footprint is consistent or inconsistent.
- Pixelscan combines a variety of features and tests into its user-friendly interface, including a VPN checker, DNS leak test, WebRTC leak test, location information detector, IP blacklist checker, bot checker, and browser fingerprint tester.
- The most common cause of inconsistency for proxy users is a timezone/language mismatch with the proxy’s IP geolocation.
- Mobile proxies produce the cleanest IP detection results because carrier-grade NAT makes them indistinguishable from real mobile traffic.
- The applications and usage of Pixelscan vary on your specific goals. A general user can rely on Pixelscan to run a browser fingerprint test for privacy reasons, while proxy users and experts might use it to validate that their IPs and browser configurations are in full alignment.
Frequently Asked Questions:
What is my browser fingerprint?
Your specific browser fingerprint is a unique identifier that is created on the basis of technical details about your browser and device. You can check and read your browser fingerprint through an analytics tool like Pixelscan.
How to check browser fingerprint?
Pixelscan is one of the top tools available to check browser fingerprint. You just have to open Pixelscan.net on your browser, click the test button, and you’ll get the results on your screen.
Can Pixelscan detect a canvas fingerprint?
Yes! Detecting and analyzing canvas fingerprint is one of the core features of Pixelscan. This includes checking if your canvas rendering matches the browser properties to identify any spoofing.
What is an anti-detect browser?
An anti-detect browser is a specialized web browser that can mask or modify a user’s browser fingerprint. It allows you to manually change the OS, browser type, plugin, timezone, and other such integral data points. Each profile appears as a unique device to websites. Antidetect browsers are typically paired with proxies to ensure the IP address matches the fingerprint configuration.
Why does Pixelscan show my fingerprint as inconsistent?
The most common reasons are: a timezone that does not match your IP geolocation, a user-agent that contradicts your hardware fingerprints, WebGL data that exposes your real GPU while your profile claims a different device, WebRTC leaking your real IP, or automation flags like navigator.webdriver being set to true. You can review the detailed breakdown in Pixelscan to identify exactly which parameters are causing the inconsistency.
How do proxies affect my Pixelscan results?
Your proxy determines the IP address, geolocation, and IP type (datacenter, residential, or mobile) that Pixelscan detects. If your proxy IP geolocates to a different region than your browser timezone and language settings, Pixelscan will flag the mismatch as inconsistent. Using high-quality residential or mobile proxies that match your profile’s configured location produces consistent results.




